MD380Tools
Back in 2015, I found a null pointer read vulnerability in the Tytera MD380, which is a fancy way to say that I could dump out the bootloader that decrypts the rest of the encrypted firmware update, and by patching that, get a clear copy of the firmware running the radio. DD4CR dropped by to visit about that time, and she managed to break the encryption, so that firmware updates from the manufacturer could be decrypted and re-encrypted without a radio.
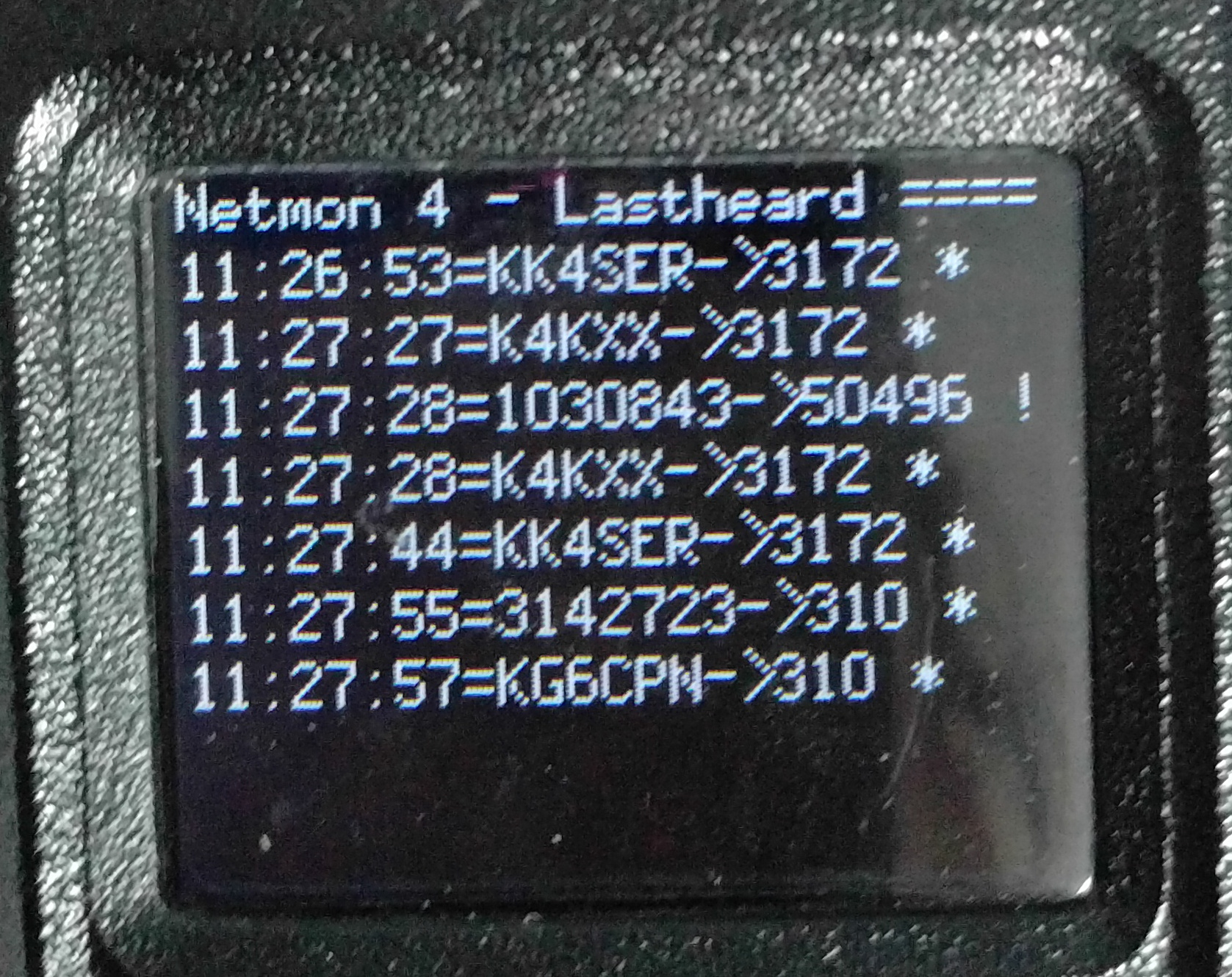
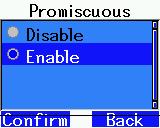
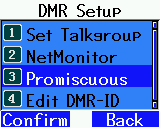
Eventually PA9TV, DF8AV, DL2MF and other fine folks joined along to create a set of patches against the vendor firmware that provide such features as promiscuous mode, a database of all registered DMR amateurs, compatibility with Motorola’s Basic Privacy mode, a call log, and raw packet capture to a monitoring desktop computer.
Source code is available on the MD380Tools github repo. Development has wound down since DF8AV went SK, but OpenGD77 has sprung up as a worthy and active successor project, building almost entirely open source firmware for the GD77 series of dual-band DMR handhelds.